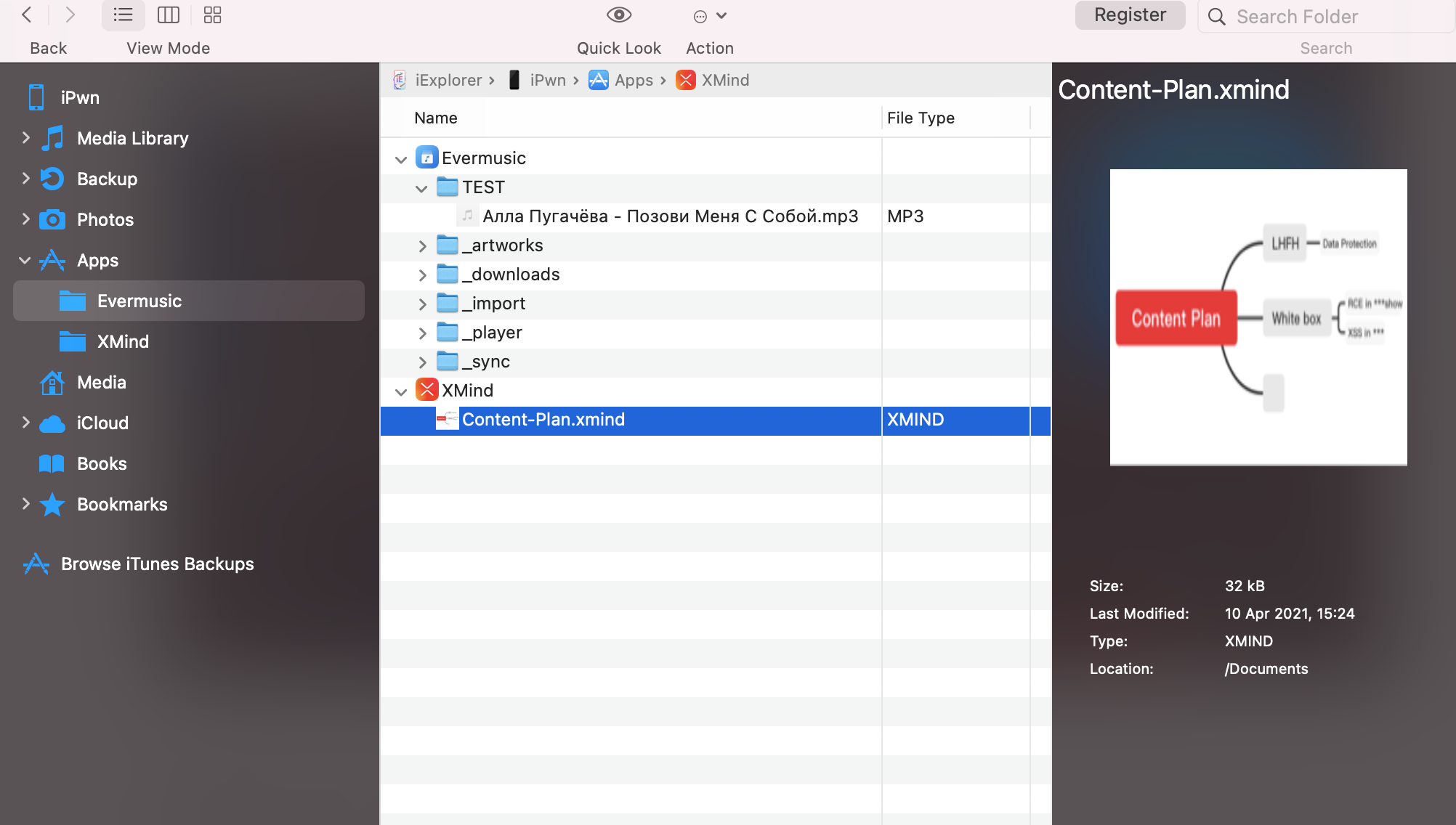
The simplest way of how to find and exploit Data Protection API misconfigurations:
- Install the demo version of iExplorer tool on any computer;
- Connect an iPhone and enable trust;
- Lock the device and disconnect the device from the computer;
- Keep the device locked, connect the device to the computer and use iExplorer tool to gather unencrypted data.
Severity: from Informational to Medium
CVSS3: up to 4.8
AV:P/AC:L/PR:H/UI:R/S:C/C:H/I:N/A:N