In web app security, a large number of clients attack the server. In client app security, the situation is opposite – a huge amount of client devices are always carried by people, that can do whatever they want, be as relaxed as they want, and still need to be protected.

Client-side threat agents
Lyhin’s Lab distinguishes four additional threat agents related to the clients, while, of course, the client is definitely a threat agent for the server. The pen test of a client application on behalf of these five threat agents is considered to be complete.
A device stealer
Main questions:
- What can a malicious actor get, if they steal the device and is capable to unlock the phone?
- What can get a malicious actor get, if they have a Remote Access Toolkit on the rooted victim’s device?
- Does the application allow the saving of sensitive data in backups? How about the cloud?
Just a friendly reminder: sometimes there’s no need to unlock the device to install applications on the victim’s phone.
A malware
Main question: What can get a regular application on a non-rooted device?
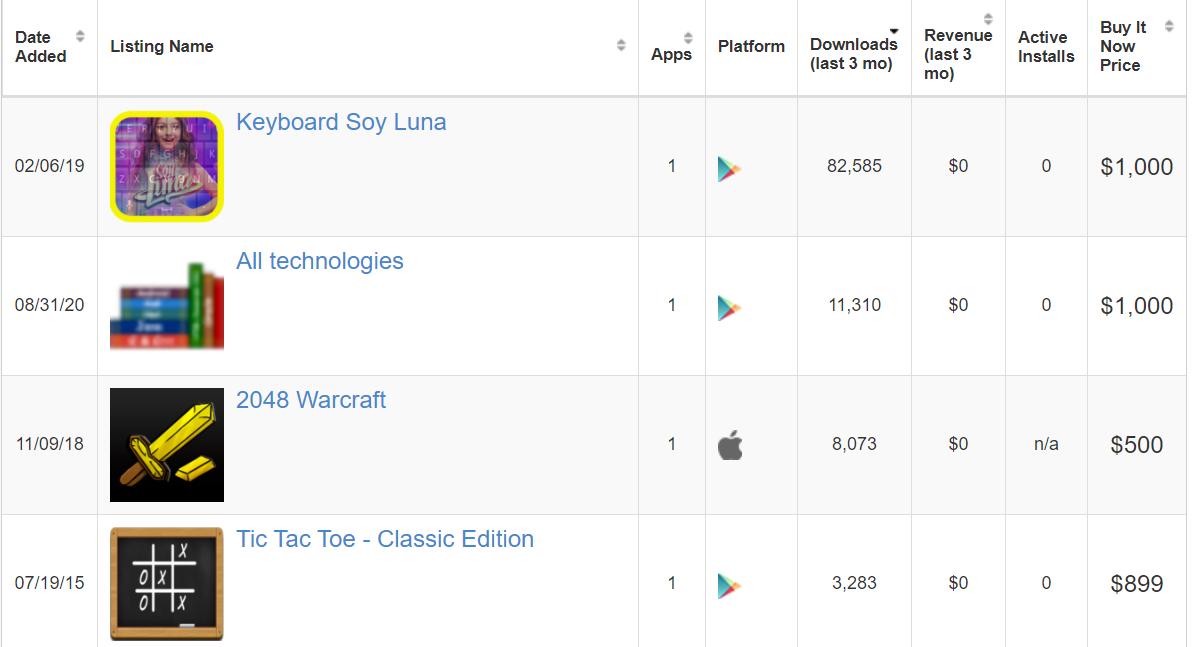
Just a friendly reminder: some applications with thousands of downloads could be bought in terms of thousands of dollars.
The application itself
The client brings danger to the server, but the server also brings danger to the client. Main questions:
- Does the application require suspicious permissions?
- Does the application collect suspicious data? How much data is being collected by the application?
Just a friendly reminder: big companies often white-list applications allowed on their devices.
An intruder
Main questions:
- What can a malicious actor do, if they control the router or the proxy-server between the device and the Internet?
- What can a malicious actor do, if they remotely interact with a user?
Just a friendly reminder: hackers can ask people to install TLS certificates.
Conclusion
Today, 17th of October, 2020, I believe that there is no other threat (Y) agent which is:
- capable to do anything that the listed agents cannot do OR
- can do something that the listed agent (X) can AND can have an evil intent that (Y) threat agent cannot have
While it seems like there is rigorous proof, I’d rather discuss it somewhere in a more private conversation. By the way, all these five threat agents could be effectively memorized on a hand. Guess how.